Unify access across humans, AI agents, and machine identities
Modern work extends beyond login sessions

Visibility breaks down on endpoints
AI tools, agents, and scripts run on devices and local environments that are easy to miss. When activity isn’t visible, exposed credentials go unaddressed.

Authorization stops at login
Authorization is often decided once, at login or setup. Access can outlast the conditions it was granted under.

Accountability falls apart across systems
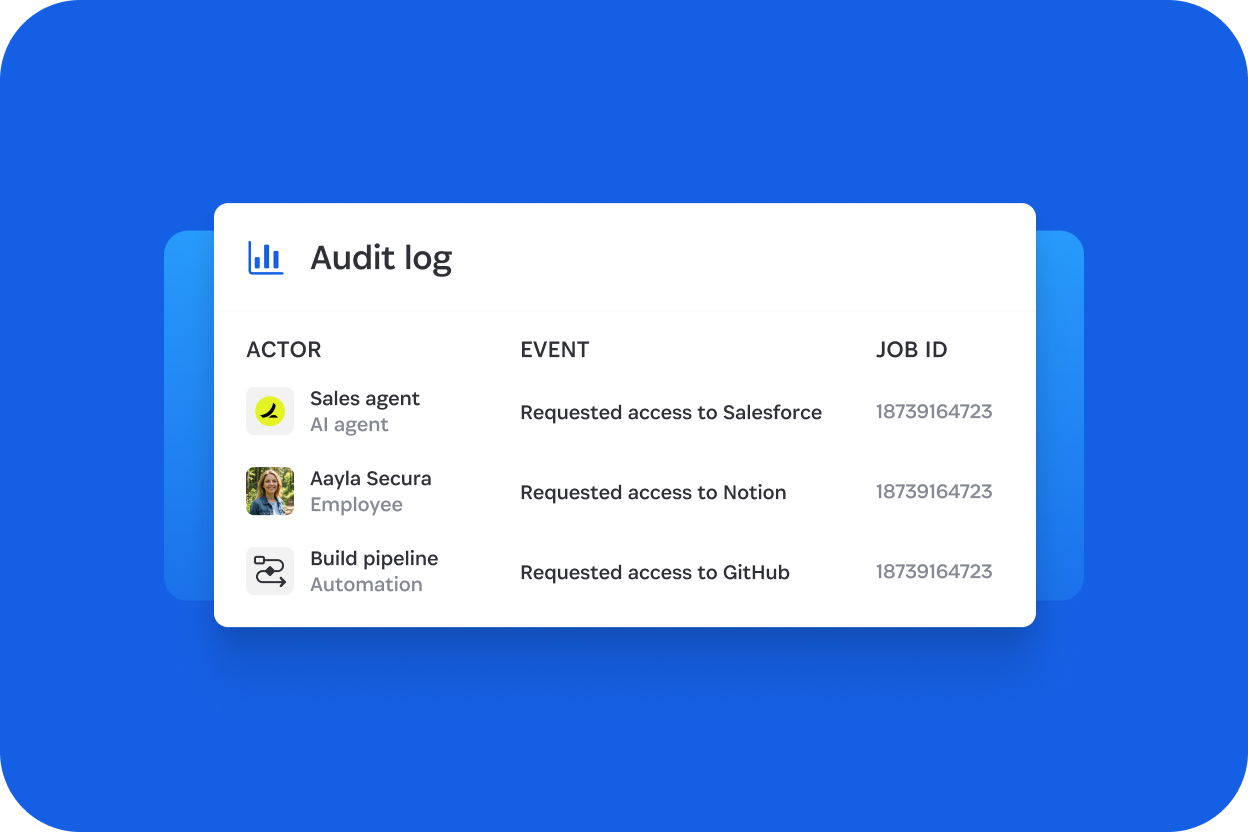
Agents inherit delegated authority without clear scope or expiration. Actions become harder to trace across systems, so proving who did what takes time.
Talk to an expert
Explore how Unified Access discovers shadow AI and exposed credentials on endpoints, then guides remediation before risk reaches CI/CD and production systems.
This interactive demo has been hidden because it needs cookies you haven't agreed to yet. Click the button below to update your cookie preferences and enable the interactive demo.
Unified Access governs how credentials and secrets are used
Discover shadow AI usage, local agents, and exposed credentials across endpoints and environments
Secure access with time-of-use control authorization before authority is exercised
Audit when, where, and under whose authority credentials and secrets were used across humans, agents, and machine identities
What Unified Access unlocks
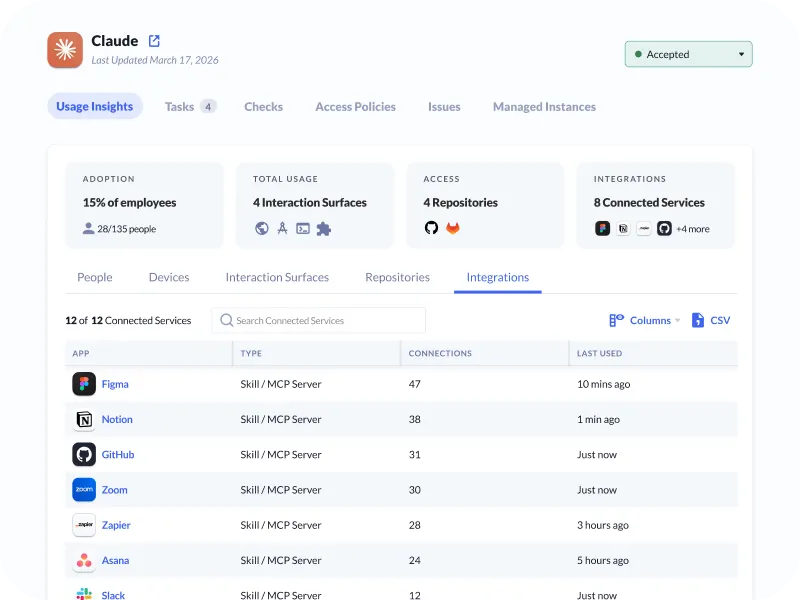
Unified AI insights
Get a consolidated view of AI tools and local agent usage across your organization to understand adoption, access risk, and exposure.
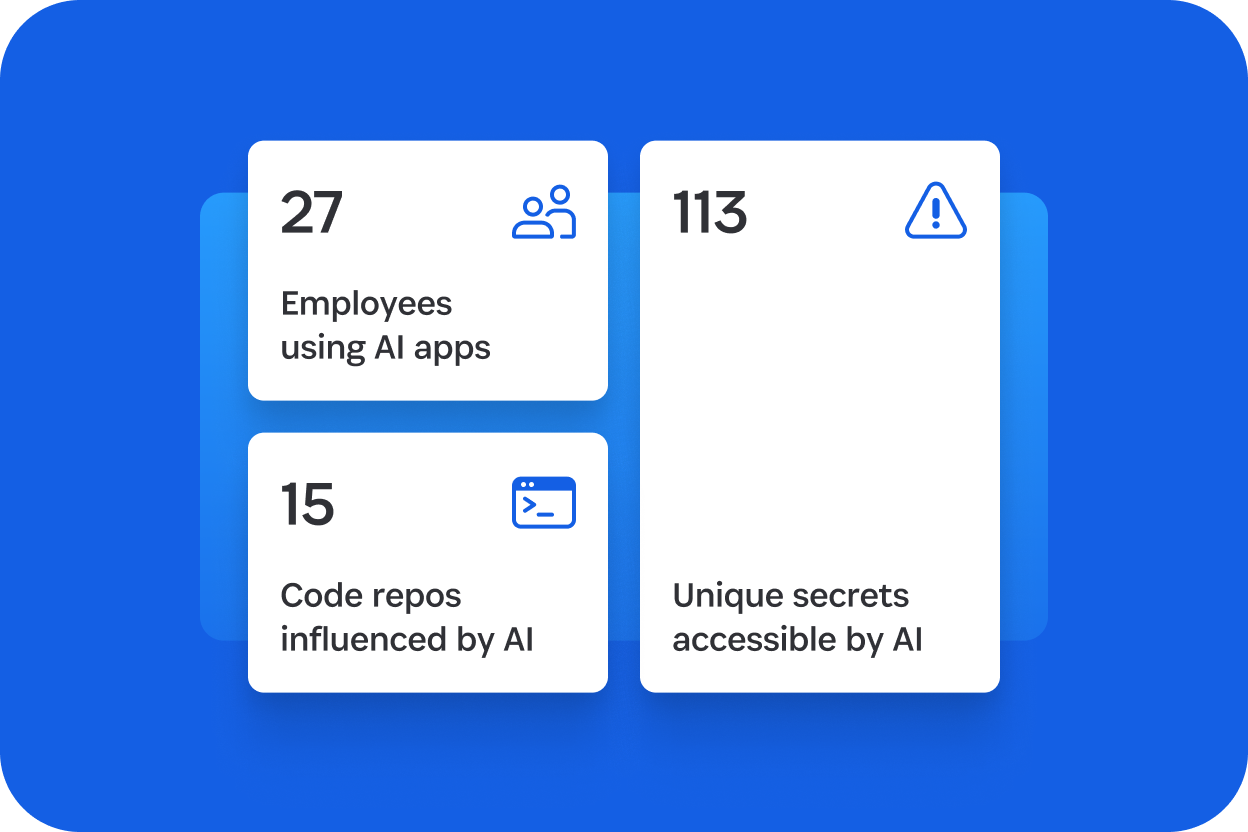
Endpoint AI discovery
Identify unmanaged AI tools and agents running on developer devices and surface unmanaged risk before it reaches shared systems.
Unsecured credential discovery
Detect credentials and secrets in local files and developer environments so teams can remediate before they reach CI/CD and production.
Guided risk remediation
Help developers vault exposed credentials, remove risky AI tools and agents, and close gaps without disrupting workflows.
Centralized secure vaulting
Store every credential type in one encrypted vault, giving you a single system of record across humans, agents, and machine identities.
Credential governance
Centralize control of high-risk and shared credentials so IT teams can define who has access without exposing the secret itself.
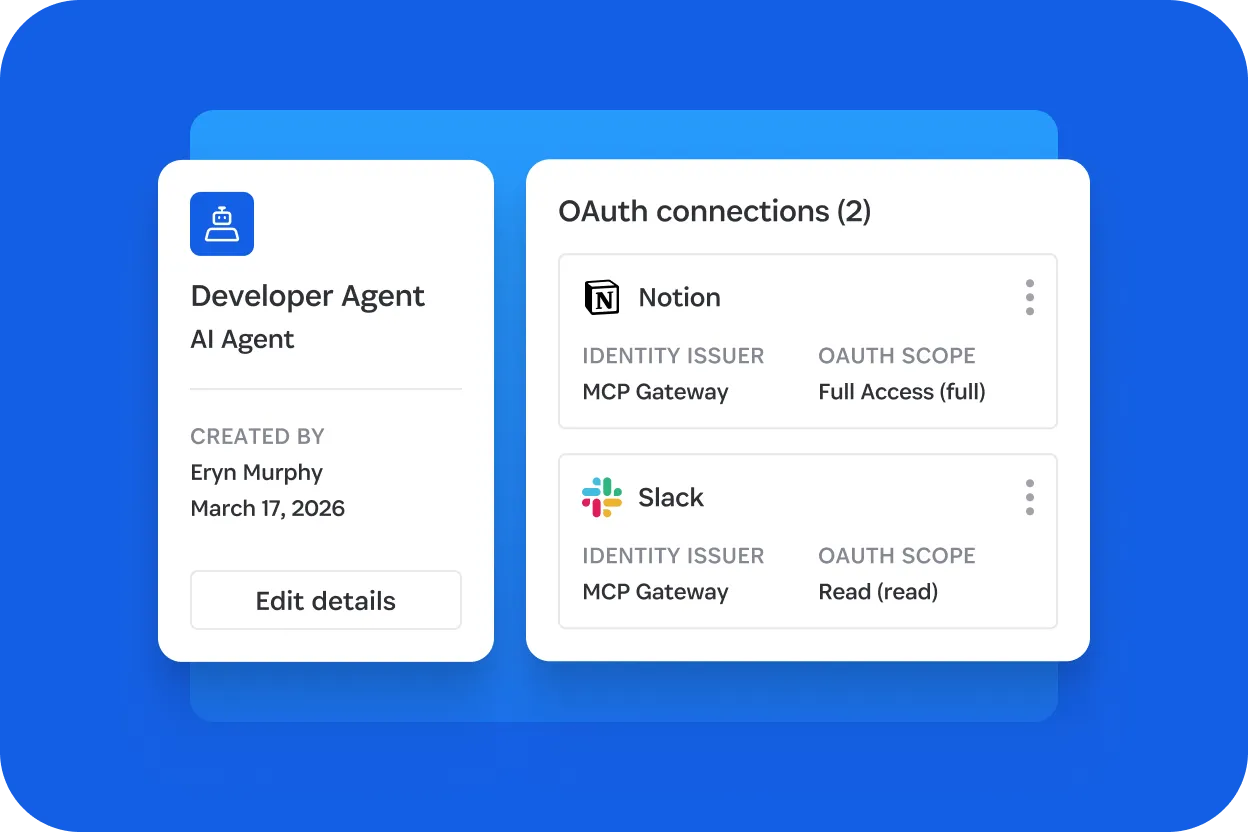
Runtime credential brokering
Deliver credentials to agents, automation, and CI/CD at runtime to reduce long-lived secrets, limit standing access, and ensure they’re used only when needed.
Unified audit logs
Provide clear attribution for every action, showing who or what used which credential, when, and under whose authority, across humans, agents, and machine identities.
Why Unified Access matters
Unified Access brings discovery, vaulting, time-of-use control, and audit into one system for secure, accountable access across humans, agents, and machine identities.
Deployed across millions of endpoints
Trusted with over 1.3B secrets
Protecting over 180,000 businesses
Get started with 1Password Unified Access
See how 1Password Unified Access helps you discover, secure, and audit credential use across endpoints, developer environments, and runtime workflows.
Frequently asked questions
What is 1Password Unified Access?
1Password Unified Access is a security solution that governs credential access across humans, AI agents, and machines. It provides endpoint discovery, centralized credential storage, runtime credential delivery, and unified attribution to reduce credential sprawl and unmanaged access.